
Washington D.C. Government Contractor Cybersecurity: Architecture for Federal Compliance
D.C.-area government contractors need cybersecurity architecture that satisfies federal compliance requirements while remaining operationally practical.
Deep technical insights on building secure systems — from penetration testing methodologies to zero trust architecture and modern security tooling decisions.

D.C.-area government contractors need cybersecurity architecture that satisfies federal compliance requirements while remaining operationally practical.

Quick Answer: Penetration testing simulates real-world cyberattacks to identify vulnerabilities in your systems before hackers exploit them. For business leaders, pen testing is essential for compliance (PCI DSS, SOC 2, HIPAA), pre-M&A due diligence, and validating security investments. Costs range from $5,000-$50,000+ depending on scope. Most organizations need annual testing at minimum, with quarterly testing …

Web applications power modern business operations, but they're also the primary target for cybercriminals. Over 90% of successful data breaches exploit web application vulnerabilities, costing organizations an average of $4.9 million per incident. The Open Web Application Security Project (OWASP) framework identifies the most dangerous application security risks that every business leader should understand. While …

Every CISO, CEO, and CFO eventually faces the same critical question: should your organization invest in SIEM vs XDR security architecture? After helping Fortune 500 companies and resource-constrained organizations evaluate these decisions through BlueRadius Cyber consulting engagements, including implementations of our Threat Ops platform, the answer isn't about the technology. It's about strategic architecture decisions …
Executive Summary: API security for business leaders isn't just a technical concern—it's a critical business imperative. With APIs handling 83% of web traffic and API-related breaches costing 23% more than average data incidents, understanding and securing your organization's API infrastructure has become essential for protecting revenue, reputation, and regulatory compliance. The digital transformation of modern …

The cybersecurity landscape has fundamentally shifted, making zero trust implementation strategies a critical priority for modern enterprises. By 2025, 60% of companies will consider Zero Trust as a security starting point, and 81% of organizations plan to implement Zero Trust strategies within the next 12 months. Yet despite this widespread adoption intent, developing effective zero …
In today's day and age, application security has never been more crucial. As technology advances, so do the tactics employed by cybercriminals, leaving applications vulnerable to a myriad of security flaws. Understanding these vulnerabilities is the first step in shielding your applications from malicious attacks. “The single biggest existential threat that’s out there, I think, …
Discover how regular penetration testing can safeguard your business from costly cyber attacks. Want to save money and enhance security? Learn more here.
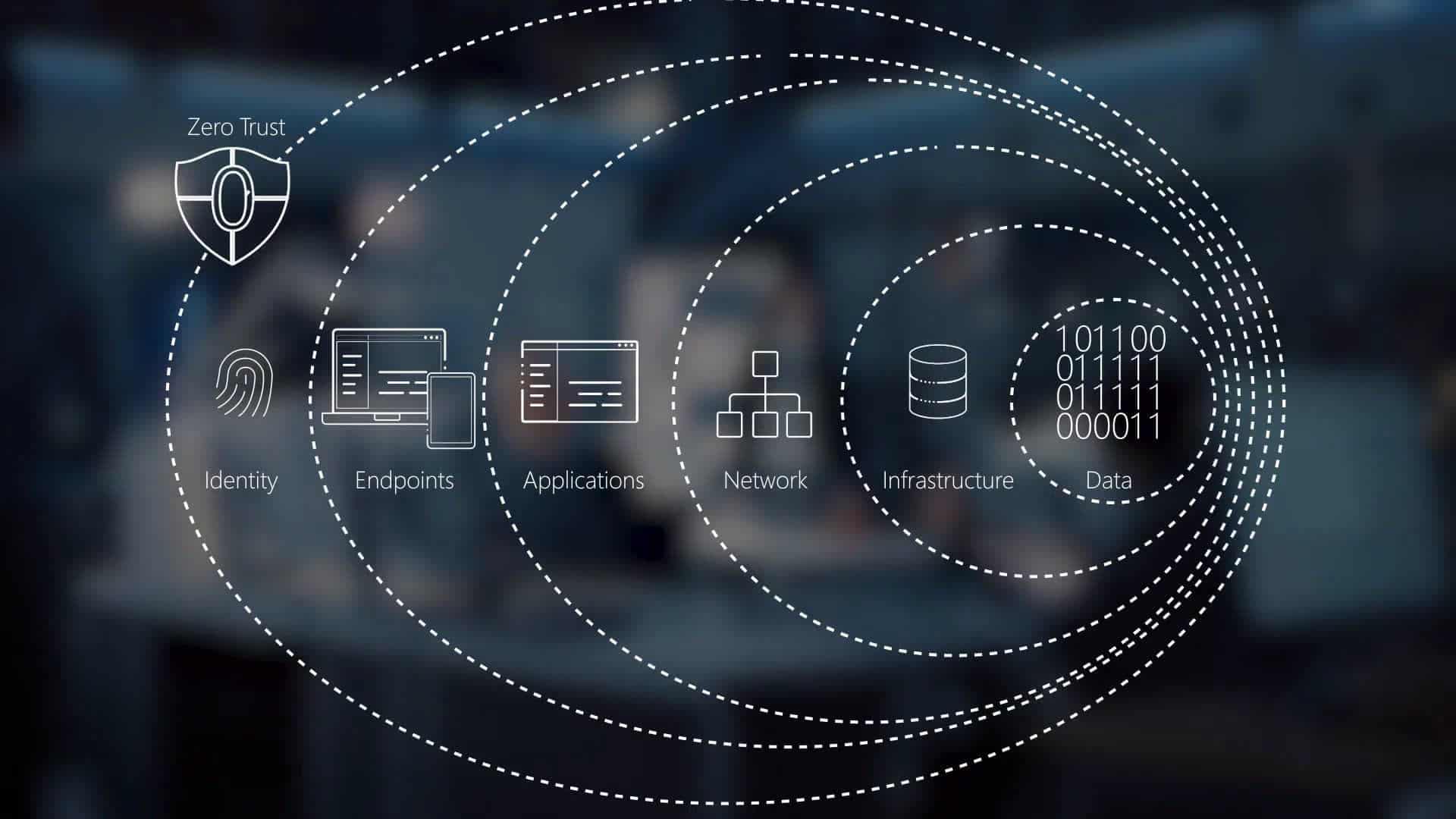
In today's digital landscape, traditional security measures are no longer sufficient to protect against evolving cyber threats. Enter Zero Trust Architecture, a security model that revolutionizes computer networking by enforcing the principle of "never trust, always verify." This comprehensive guide explores the core components of Zero Trust, its implementation best practices, and real-world case studies, illustrating how this approach can significantly enhance security, reduce risks, and ensure data integrity in various digital environments. Learn how adopting Zero Trust Architecture can transform your organization's security posture and safeguard your critical assets.