Enterprise Product Security in the Age of Claude Code: What Security Leaders Must Do Now
When Anthropic launched Claude Code Security, public cybersecurity stocks sold off hard. CrowdStrike and Cloudflare fell roughly 8%. Okta and SailPoint dropped around 10%. Israel’s JFrog shed nearly 25% in a single session. The easy headline wrote itself: AI just killed cybersecurity.
That narrative is wrong, but it is pointing at something real that every enterprise security leader needs to act on right now, specifically in product security.
What Claude Code Security actually did was expose a structural gap that has quietly been widening for years: most enterprise product security programs were built for a world where developers ship code slowly, security reviews happen after the fact, and humans are the primary reasoning engine for vulnerability triage. That world is gone. The gap is now public knowledge, and your board will be asking about it soon.
This post is for CISOs, security architects, and virtual CISOs who need to understand what changed, what it means for their product security program, and what a modern response looks like before the window closes.
What Claude Code Security Actually Signals
Anthropic’s tool is code-focused, but the signal is far broader than application security tooling. A frontier AI lab shipped a security workflow that resembles reasoning and remediation far more than it resembles rules and alerts. That is a fundamentally different architecture than most enterprise product security programs are built around today.
Traditional product security stacks optimize around three activities: scanning (SAST, DAST, SCA), alerting security teams to findings, and managing a remediation backlog that engineering teams work through on their own schedule. The implicit assumption embedded in that model is that humans have enough time to reason through findings before the threat landscape shifts.
Agentic AI tools have invalidated that assumption at the development layer, and the disruption is now spreading into the security layer. Software is being written, refactored, and shipped at a velocity that manual review cycles simply cannot match. Attack discovery and exploitation are compressing simultaneously, because the same AI capabilities that help defenders find vulnerabilities also help adversaries chain and exploit them faster.
The result is a shrinking detection-to-response window across the entire product security lifecycle. If you want a plain-language breakdown of the terms and frameworks referenced throughout this post, our cybersecurity glossary is a useful reference.
The Three Forces Colliding in Enterprise Product Security
Understanding why product security is under pressure requires looking at three forces that are accelerating simultaneously.
Software velocity has outpaced security review cadence. Agentic development tools are compressing sprint cycles. Code is written faster, shipped more frequently, and reviewed with less consistency. Every acceleration in development velocity is a corresponding increase in the rate at which unreviewed risk enters production. Most enterprise product security programs scale linearly, adding headcount or scanning tools, but the underlying risk is growing exponentially with software volume.
The attack surface is expanding into every integration and data source. Modern enterprise applications are not standalone systems. They pull from SaaS APIs, CI/CD pipelines, cloud configuration layers, third-party SDKs, and LLM integrations. Each connection point is a potential attack vector, and the signals from each flow into a different tool with a different alert taxonomy. Security teams are buried in noise they cannot correlate fast enough to stop real incidents before they escalate. Our threat operations capability exists specifically to address this correlation gap, moving organizations from reactive alert triage to continuous, proactive threat detection across every data source.
AI has lowered the barrier to sophisticated attack execution. The same reasoning capabilities that allow Claude Code Security to identify vulnerabilities in a codebase allow adversarial actors to automate reconnaissance, chain vulnerabilities across integration boundaries, and conduct phishing and social engineering at a scale and personalization level that was previously impossible without large teams. We covered the most critical attack patterns affecting enterprise organizations in our analysis of top cyber threats disrupting business operations.
Together, these three forces mean that the scan-alert-backlog model of product security is not just inefficient. It is structurally unable to protect organizations operating at modern software velocity.
What a Modern Enterprise Product Security Program Looks Like
The architecture of effective product security is knowable. It requires rethinking four foundational elements.
Security must move left and stay left. Shift-left is not a new concept, but most organizations treat it as a tooling decision: drop a SAST scanner into the CI/CD pipeline and call it done. Genuine shift-left product security means embedding security requirements, threat modeling, and security acceptance criteria into the earliest stages of the product development lifecycle, before a line of code is written. It means security engineers participating in design reviews, not just scan results. And it means developer security training that is contextual and continuous, not annual checkbox compliance. Our cybersecurity awareness training guide covers the training architecture that supports this kind of embedded security culture.
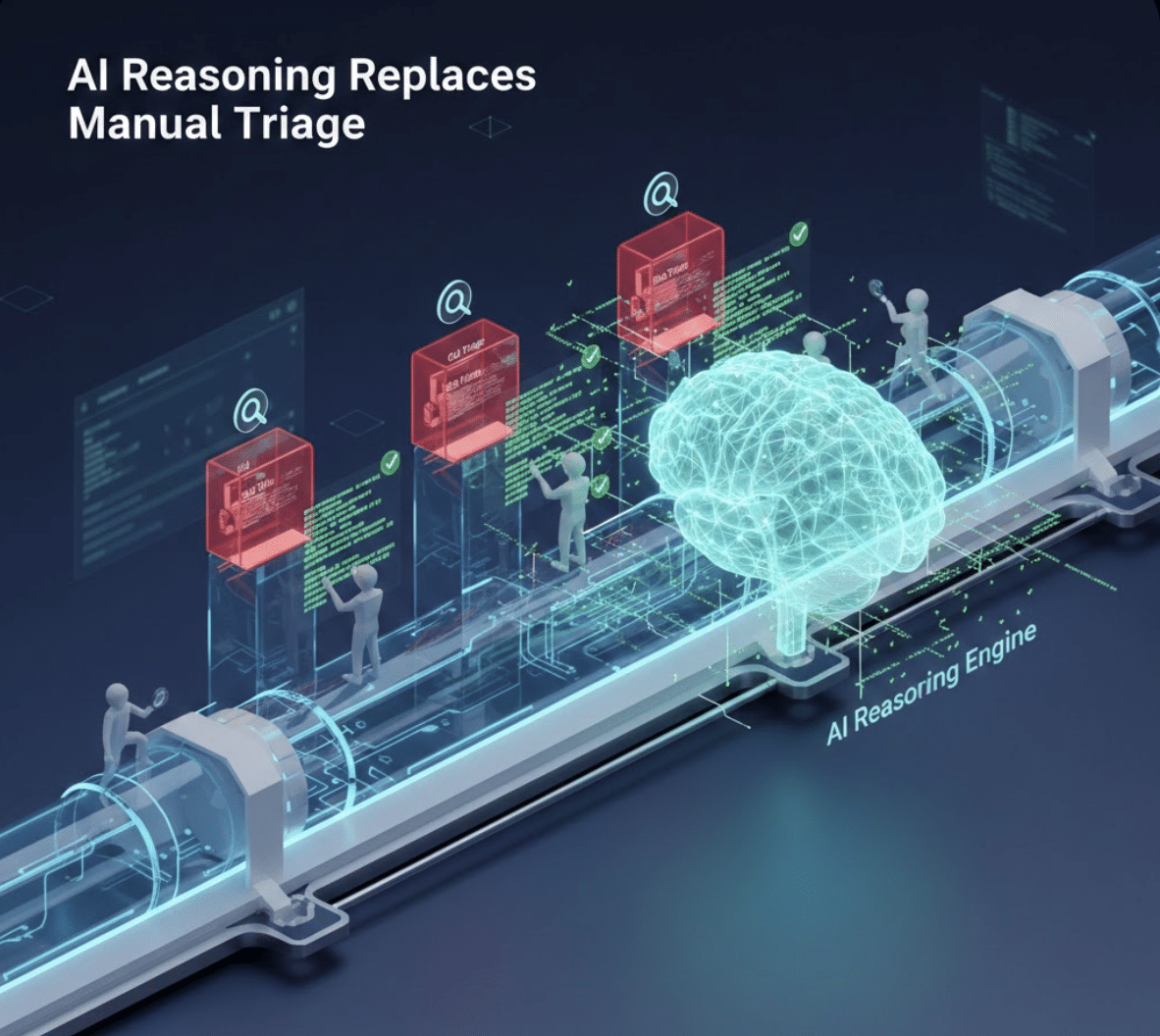
AI-assisted vulnerability reasoning must replace manual triage. The bottleneck in most enterprise product security programs is not scanner coverage. It is the human reasoning capacity to evaluate findings, understand exploitability in context, prioritize against business risk, and route remediation to the right team with enough information to act quickly. Our AI security services are built around exactly this capability gap, helping organizations implement AI-assisted triage and remediation workflows with the governance guardrails required for enterprise accountability. If you want to understand how we approach AI security architecturally, our AI governance guide for vCISOs is the right starting point.
Product security must integrate with your broader security architecture. Vulnerability findings in the codebase mean something different when correlated with runtime anomaly data, identity and access activity, cloud configuration drift, and live threat intelligence about active exploitation of that vulnerability class. Enterprise organizations that treat product security as an isolated program, siloed from SOC operations, identity governance, and cloud security, are making prioritization decisions with incomplete context. Our managed security services provide the integrated monitoring layer that connects product security findings to the broader enterprise security fabric, giving security teams a unified view instead of disconnected tool outputs. For organizations that need structured GRC tooling to tie this together, our Radius360 platform provides the compliance and governance backbone that keeps program management auditable and board-ready.
Security governance must scale to board-level accountability. Your board has questions about AI and software risk that they have not yet figured out how to ask. Product security risk, meaning the risk that vulnerabilities in your software create liability, compliance exposure, or reputational harm, is now a board-level issue in the same way ransomware resilience became one after high-profile incidents. Our cybersecurity board reporting guide provides the framework for translating technical program maturity into business risk language that boards can act on. And for organizations subject to regulatory frameworks such as HIPAA, CMMC, SOC 2, or state-level breach notification requirements, our regulatory compliance services ensure that product security program documentation meets the evidentiary standard regulators expect.
Claude Code Security and the vCISO Opportunity
One of the most important dynamics in the current moment is the position it creates for organizations operating with a virtual CISO model. Many mid-market enterprises, the exact organizations that are rapidly adopting AI development tools and expanding their software surface, do not have the in-house expertise to evaluate what Claude Code Security means for their security posture, let alone build a coherent response.
This is precisely the expertise gap that a fractional or virtual CISO fills. A vCISO with product security depth can help organizations answer four critical questions right now.
Where in your SDLC is your greatest uncontrolled risk exposure given your current development velocity? This requires a security architecture review that maps your development lifecycle against your threat model, not just a scan of your current codebase. Our security risk assessment guide walks through the methodology we use to answer this question for new clients.
Which AI development tools are your engineering teams already using, and what are the security implications of each? Our GitHub Copilot security review covers one major tool in depth, but most organizations need a broader AI tool inventory before they can answer this question comprehensively.
How do your existing application security controls need to evolve to provide meaningful coverage in an AI-assisted development environment? Most SAST and DAST tools were not designed around the code patterns that AI code generators produce at scale. Our application security testing services are structured to evaluate this gap and recommend controls that perform in AI-augmented development environments.
How do you communicate the state of your product security program to your board, customers, and regulators in a way that builds confidence? We address the communication architecture in detail in our board reporting guide, and you can see how we have applied this approach across industries in our case studies.
A skilled vCISO structures the answers to these questions into a 90-day transformation roadmap your organization can execute without rebuilding your entire security stack. Our vCISO implementation guide details exactly what that 90-day engagement looks like in practice.
The Industries Feeling This Pressure Most
Product security disruption is not uniformly distributed across sectors. The organizations feeling the most acute pressure share two characteristics: they produce or heavily depend on software as part of their core product or service delivery, and they operate under regulatory frameworks that increasingly require demonstrable security program maturity.
In financial services, AI-assisted development has accelerated the introduction of new application features while simultaneously increasing the complexity of the attack surface regulators are scrutinizing. Our Dallas financial services cybersecurity analysis covers the specific compliance and product security pressures facing banks and credit unions in the current environment.
In healthcare, the combination of legacy application debt, rapid telehealth expansion, and strict HIPAA requirements creates a product security environment where the stakes of a vulnerability are not just financial but directly patient-facing. Our HIPAA compliance checklist addresses the compliance dimension, while our broader Dallas healthcare cybersecurity work illustrates the implementation complexity these organizations face.
In energy and critical infrastructure, operational technology increasingly shares integration points with IT software stacks, creating product security exposure that legacy OT security frameworks were never designed to address. Our oil and gas cybersecurity analysis covers the specific threat landscape and control requirements for this sector.
For a full view of the industries and markets we serve, our markets we serve page provides sector-specific context. And for organizations earlier in their security maturity journey, our cybersecurity services for SMBs in critical sectors addresses the specific product security constraints facing smaller organizations operating in regulated environments.
What the Market Disruption Means for Enterprise Security Buyers
The stock sell-off that followed Claude Code Security’s launch was a market signal, not a verdict on the future of enterprise security spending. What the market was actually pricing was a reset in where security value accrues.
Products that primarily generate alerts, rules, and dashboards without providing correlated, prioritized, actionable output are under genuine pressure. Organizations are going to increasingly ask whether a tool that surfaces 4,000 low-context vulnerability findings per month is actually reducing their risk or simply shifting liability to the engineering backlog.
Products and services that ingest multiple security data sources, correlate findings reliably, prioritize with explainable evidence, and execute remediation with appropriate human oversight and auditability: those are the capabilities that will define enterprise security programs in an AI-speed environment. Our SIEM vs. XDR architecture guide addresses the core architectural decision most organizations face as they evaluate how to rebuild their security data layer for this environment.
Our vCISO market report documents how the role of security leadership itself is evolving in response to these pressures, and why organizations that invest in strategic security leadership now will have a measurable advantage as the market resets.
For a deeper dive into the economics of this investment, our analysis of evaluating ROI on cybersecurity consulting provides the financial framework for making the business case internally.
Building Your Product Security Response: Where to Start
If you are trying to operationalize a response to this moment, a practical starting framework has three phases.
In the first 30 days, conduct an honest inventory. Map every AI tool your developers are using. Assess your current SDLC security coverage against your actual software development velocity, not a theoretical deployment cadence. Identify the three highest-risk integration points in your production software stack. This does not require new tooling. It requires dedicated analysis time from someone with product security expertise. Our free cybersecurity assessment is specifically designed to give organizations an honest starting-point baseline without a long procurement cycle.
In days 30 through 60, address your highest-risk gaps with targeted controls. This typically means tightening security gates in your CI/CD pipeline, establishing an AI tool usage policy with specific security guardrails, and conducting threat modeling on your highest-value application assets if it has not been done in the past 12 months. Organizations that are new to structured security program development may find our cybersecurity starter kit useful for establishing baseline controls before layering product security-specific practices on top.
In days 60 through 90, build the governance layer. Establish product security KPIs your board can understand and track. Create a communication cadence that keeps engineering and security leadership aligned on risk prioritization. Document your product security program maturity in a format that supports customer trust conversations and regulatory inquiry. Our library of cybersecurity white papers includes frameworks for program documentation that meet the standard regulators and enterprise customers expect.
For ongoing intelligence on how the product security landscape continues to evolve, our Cyber Insights hub aggregates practitioner analysis across the threat, compliance, and technology dimensions. And if you have perspective to contribute from your own organization, our guest cybersecurity blog program welcomes submissions from experienced security professionals.
The Bottom Line for Enterprise Security Leaders
Anthropic did not kill cybersecurity. It validated that frontier AI is now a genuine participant in the security market at exactly the moment when software velocity, attacker capability, and data complexity are all accelerating.
For enterprise product security programs, that validation changes the stakes. The organizations that will emerge from this transition in the strongest position are the ones that treat Claude Code Security’s launch not as a threat to their security budgets, but as a forcing function for modernizing programs that were overdue for transformation anyway.
CISOs are not being replaced. They are being handed a new mandate: run product security at machine speed, across more systems, with less tolerance for noise, and with board-level accountability for outcomes.
Blue Radius Cyber has built its practice around exactly this mandate, combining virtual CISO leadership, managed security operations, threat operations, and AI-integrated security services into programs that enterprise organizations can execute without building a full in-house security function from scratch. You can learn more about how we work and the team behind the practice on our about us page, and review our coverage in enterprise security media on our press page.
Ready to assess your enterprise product security program against modern AI-speed threats? Start with a free cybersecurity assessment, or if you know an organization that needs this conversation, our cybersecurity referral program rewards introductions that lead to meaningful security improvements.

Jeff Sowell is a cybersecurity leader with over 20 years of experience in IT and security roles at Fortune 500 companies. He has held key positions such as VP, CISO, and CPSO, serving as Head of Product Security at Ericsson North America. Jeff holds an M.S. in Computer Information Systems (Security) from Boston University and industry-recognized certifications including CISSP, CISM, and ISO 27001 Lead Implementor.
Related from the BlueRadius Library
Sourced posts on adjacent topics, ranked by tag overlap.
AI Security
Bay Area AI Security & Governance: Protecting ML Models and Training Data
Bay Area AI companies need security governance for ML models, training data, and AI pipelines. Protect intellectual property and meet emerging AI compliance requirements.
ReadAI Security
GitHub Copilot Security Review: Complete Guide for Development Firms (2025)
Seven specific security risks of GitHub Copilot adoption at enterprise scale, drawn from real-world security incidents. Code provenance, training data exposure, secrets leakage, li
ReadAI Security
Proactive Threat Hunting with AI-Powered BlueRadius Threat Ops
Most security teams are stuck in an endless cycle of alerts, dashboards, and damage control. An alert fires. Analysts dig through fragmented logs, dashboards, and tickets—often for
ReadRelated services