Virtual CISO Implementation Guide: What to Expect in Your First 90 Days
You’ve made the decision to engage a virtual CISO for your organization. You’ve completed the selection process, signed the contract, and now you’re wondering: what actually happens next?
If you’re still evaluating virtual CISO providers, consider starting with a free cybersecurity assessment to understand your current security posture and implementation requirements.
The first 90 days of a virtual CISO engagement are critical to long-term success. Unlike hiring a full-time employee who gradually learns your business, a virtual CISO must quickly assess your current security posture, identify immediate risks, and begin building strategic improvements—all while establishing trust with your team and stakeholders.
This guide provides a realistic timeline of what to expect during your virtual CISO implementation, from the initial security assessment through the establishment of ongoing security program management.
Understanding Virtual CISO Implementation Success
Virtual CISO implementations succeed when three key elements align: clear expectations, structured process, and collaborative partnership. Organizations that approach the engagement with realistic timelines and defined success metrics typically see measurable security improvements within 60-90 days.
The implementation process differs significantly from traditional consulting engagements. Instead of delivering a final report and departing, your virtual CISO becomes an ongoing strategic partner who must understand your business operations, risk tolerance, compliance requirements, and growth objectives to provide effective guidance.
Successful implementations require active participation from your internal team. Your virtual CISO brings cybersecurity expertise and strategic guidance, but cannot implement changes without collaboration from IT staff, management, and key stakeholders across your organization.
Pre-Implementation Phase: Setting the Foundation
Contract Finalization and Scope Definition
Before your virtual CISO begins active work, expect to complete several administrative and planning activities. These typically include finalizing service agreements, defining reporting structures, establishing communication protocols, and identifying key stakeholders for the engagement.
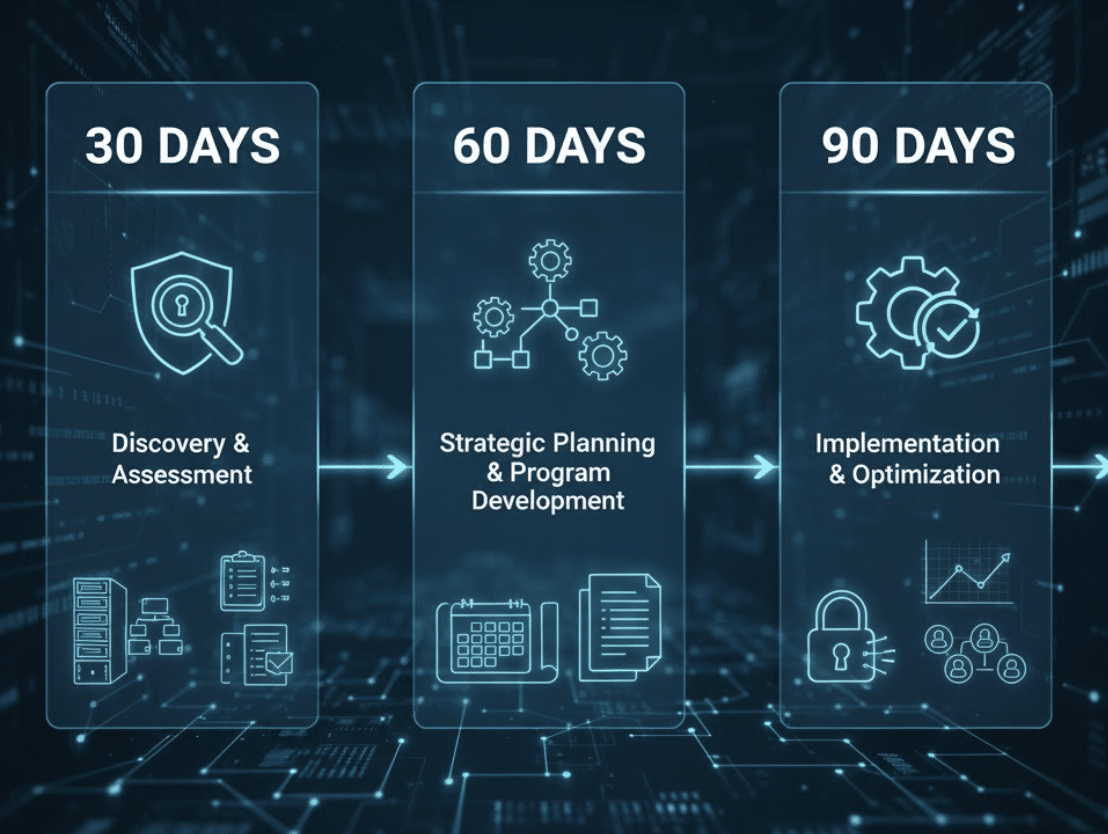
Your virtual CISO provider should clearly document the scope of services, deliverables timeline, and success metrics during this phase. Well-structured engagements include specific milestones for the first 30, 60, and 90 days to ensure both parties maintain aligned expectations.
Initial Stakeholder Identification
Your virtual CISO will need to identify and establish relationships with key stakeholders across your organization. This typically includes executive leadership, IT management, compliance personnel, legal counsel, and department heads who manage sensitive data or systems.
Expect initial conversations focused on understanding your business model, current security concerns, regulatory requirements, and strategic objectives. Your virtual CISO should ask detailed questions about your technology infrastructure, data flows, vendor relationships, and past security incidents.
Access and Credential Setup
During the pre-implementation phase, you’ll need to provide your virtual CISO with appropriate access to assess your current security posture. This may include read-only access to security tools, network documentation, policy documents, and compliance reports.
Most virtual CISO providers follow least-privilege access principles, requesting only the minimum access necessary to complete their assessment and ongoing responsibilities. Expect discussions about secure communication methods, document sharing protocols, and access management procedures.
Days 1-30: Discovery and Initial Assessment
Comprehensive Security Posture Assessment
The first month focuses primarily on understanding your current cybersecurity posture through systematic discovery and assessment activities. Your virtual CISO will conduct interviews with key personnel, review existing documentation, and analyze your technology infrastructure to identify immediate risks and opportunities for improvement.
This assessment typically includes evaluation of your network security controls, endpoint protection, data backup systems, access management, vendor security, and incident response capabilities. Your virtual CISO should also review any existing policies, procedures, and compliance documentation to understand your current security program maturity.
Many organizations benefit from managed security services alongside virtual CISO guidance to ensure comprehensive security coverage during this assessment phase.
Expect your virtual CISO to request documentation including network diagrams, system inventories, vendor contracts, insurance policies, and any previous security assessments or audit reports. This information helps establish a baseline understanding of your security environment.
Risk Identification and Prioritization
During the first 30 days, your virtual CISO will identify and document security risks across your organization. This includes technical vulnerabilities, policy gaps, compliance deficiencies, and operational security concerns.
Rather than simply listing every possible risk, an experienced virtual CISO prioritizes findings based on your business impact, likelihood of occurrence, and cost of remediation. This risk-based approach ensures limited resources focus on addressing the most critical security gaps first.
Expect regular communication during this phase as your virtual CISO asks follow-up questions, clarifies findings, and validates their understanding of your business operations and technology environment.
Initial Quick Wins Implementation
While conducting the comprehensive assessment, your virtual CISO should identify and implement immediate security improvements that require minimal cost or effort. These “quick wins” demonstrate early value and often address obvious security gaps.
Common quick wins include enabling multi-factor authentication for critical systems, updating security software configurations, removing unnecessary user access, or implementing basic security awareness measures. These improvements provide immediate risk reduction while longer-term strategic initiatives are being planned.
Organizations in regulated industries like manufacturing or healthcare often see quick compliance improvements during this phase through basic security control implementation.
Your virtual CISO should communicate these quick wins clearly, explaining the security benefit and any operational impact to your team. This early success builds confidence in the virtual CISO relationship and establishes momentum for larger initiatives.
Stakeholder Communication and Relationship Building
The first month requires significant relationship building as your virtual CISO establishes credibility and trust with your team. Expect regular communication through scheduled meetings, informal conversations, and progress updates.
Your virtual CISO should adapt their communication style to different audiences, providing technical details to IT staff while focusing on business impact and risk for executive leadership. This multi-level communication is essential for building organization-wide support for security initiatives.
Successful virtual CISOs invest time in understanding your company culture, decision-making processes, and communication preferences during this initial period. This cultural alignment significantly impacts the long-term success of the engagement.
Days 31-60: Strategic Planning and Program Development
Comprehensive Security Program Roadmap
The second month transitions from assessment to strategic planning. Your virtual CISO will develop a comprehensive roadmap that addresses identified risks while supporting your business objectives and growth plans.
This roadmap typically includes short-term tactical improvements, medium-term strategic initiatives, and long-term program maturation goals. Expect detailed timelines, resource requirements, budget estimates, and success metrics for each recommended initiative.
Your virtual CISO should present this roadmap to executive leadership for review, discussion, and approval. The planning process should be collaborative, incorporating your feedback, budget constraints, and business priorities into the final strategic plan.
Policy and Procedure Development
During the second month, your virtual CISO will begin developing or updating essential security policies and procedures based on assessment findings and compliance requirements. This typically includes foundational policies for data protection, access management, incident response, and vendor security.
Policy development should reflect your actual business operations rather than generic templates. Your virtual CISO should work with relevant stakeholders to ensure policies are practical, enforceable, and aligned with your operational capabilities.
Expect iterative review processes as draft policies are refined based on feedback from legal counsel, IT management, and business stakeholders. Well-developed policies provide the foundation for consistent security practices across your organization.
Compliance Gap Analysis and Remediation Planning
If your organization must meet specific compliance requirements, your virtual CISO will conduct detailed gap analysis against relevant standards during this phase. This may include SOC 2 compliance consulting, HIPAA compliance for healthcare organizations, PCI DSS, GDPR, or industry-specific regulations.
The compliance analysis should identify specific requirements, document current implementation status, and develop remediation plans for any gaps. Your virtual CISO should provide realistic timelines and resource estimates for achieving compliance objectives.
Expect regular updates on compliance progress and coordination with legal counsel, auditors, or other compliance professionals as needed. Compliance initiatives often drive significant security improvements while addressing regulatory requirements.
Vendor and Technology Evaluation
Based on assessment findings, your virtual CISO may recommend new security technologies or vendor services to address identified gaps. During the second month, expect evaluation of potential solutions including cost-benefit analysis and implementation planning.
Your virtual CISO should provide objective vendor recommendations based on your specific requirements, budget constraints, and operational capabilities. This may include security tools, managed services, training programs, or consulting services for specialized needs.
For organizations requiring ongoing security monitoring, integrating 24/7 security operations center (SOC) services with virtual CISO guidance often provides comprehensive security coverage.
Technology evaluation should consider integration with existing systems, ongoing operational requirements, and total cost of ownership. Your virtual CISO should manage vendor demonstrations and proposal processes to ensure you receive appropriate solutions at competitive pricing.
Days 61-90: Implementation and Optimization
Security Initiative Implementation
The final month of initial implementation focuses on executing high-priority security initiatives identified during the assessment and planning phases. This typically includes deploying new security tools, implementing policy changes, and establishing new operational procedures.
Your virtual CISO will coordinate implementation activities with your IT team, ensuring minimal business disruption while achieving security objectives. Expect detailed project plans, timeline management, and regular progress updates during this phase.
Implementation activities should be carefully sequenced to avoid conflicts or operational issues. Your virtual CISO should provide change management support and user training as needed to ensure successful adoption of new security measures.
Incident Response Planning and Testing
During the third month, your virtual CISO will typically develop or update your incident response plan based on assessment findings and current threat landscape. This includes defining response procedures, communication protocols, and recovery processes.
Expect tabletop exercises or incident simulations to test your response capabilities and identify areas for improvement. These exercises help validate your incident response plan while building team confidence and coordination.
Your virtual CISO should coordinate incident response planning with relevant stakeholders including IT staff, legal counsel, insurance providers, and executive leadership. Effective incident response requires clear roles, responsibilities, and decision-making authority.
Ongoing Program Management Establishment
By the end of 90 days, your virtual CISO should establish sustainable processes for ongoing security program management. This includes regular reporting, continuous monitoring, periodic assessments, and strategic planning cycles.
Expect development of security metrics and key performance indicators that provide visibility into your security posture and program effectiveness. Regular reporting should include both technical security measures and business-relevant risk indicators.
Your virtual CISO should establish processes for maintaining security program currency including policy reviews, technology updates, threat intelligence integration, and compliance monitoring. These ongoing activities ensure continued security effectiveness as your business evolves.
Performance Review and Optimization
The 90-day milestone provides an opportunity to evaluate virtual CISO performance and optimize the engagement for continued success. Expect formal review discussions covering deliverable quality, communication effectiveness, and overall value provided.
This review should include feedback from multiple stakeholders including executive leadership, IT staff, and other personnel who interact with your virtual CISO. Honest feedback helps optimize the relationship and ensures continued alignment with your expectations.
Use this review to adjust communication frequency, reporting formats, project priorities, or engagement scope based on your experience during the initial implementation period. Successful virtual CISO relationships evolve based on changing business needs and stakeholder feedback.
Common Implementation Challenges and Solutions
Resource Coordination and Availability
One of the most common implementation challenges involves coordinating resources and stakeholder availability for assessment activities, planning meetings, and implementation tasks. Organizations with limited IT staff or competing priorities may struggle to support virtual CISO initiatives effectively.
Address this challenge by establishing clear expectations for internal resource requirements during the engagement planning phase. Your virtual CISO should provide realistic estimates of time commitments needed from your team and help prioritize activities based on available resources.
Consider designating a primary internal contact to coordinate with your virtual CISO and manage internal resource scheduling. This coordination role helps ensure smooth communication and reduces scheduling conflicts that can delay implementation progress.
Expectation Management and Timeline Adjustments
Virtual CISO implementations occasionally face timeline adjustments due to unexpected findings, resource constraints, or changing business priorities. Organizations with unrealistic expectations for rapid transformation may become frustrated with implementation pace.
Maintain realistic expectations by understanding that comprehensive security program development requires time and sustained effort. Your virtual CISO should provide honest assessments of timeline feasibility and recommend adjustments when circumstances change.
Regular communication about progress, challenges, and timeline adjustments helps maintain stakeholder confidence and ensures alignment between expectations and reality. Transparency about implementation challenges builds trust and supports long-term success.
Technology Integration and Operational Impact
Implementing new security technologies or procedures may create operational challenges as your team adapts to new processes and tools. Resistance to change or inadequate training can impact implementation success.
Address integration challenges through comprehensive change management including user training, gradual rollout processes, and ongoing support. Your virtual CISO should coordinate closely with your IT team to minimize operational disruption.
Consider piloting new technologies or procedures with limited scope before full implementation. This approach allows identification and resolution of integration issues before broader deployment.
Setting Success Metrics and Expectations
Measurable Security Improvements
Successful virtual CISO implementations should produce measurable security improvements within the first 90 days. These may include reduced vulnerability counts, improved security tool coverage, enhanced policy compliance, or stronger access controls.
Work with your virtual CISO to establish specific, measurable success criteria for the initial implementation period. These metrics should reflect your most important security priorities and provide clear visibility into progress.
Regular measurement and reporting of security improvements helps demonstrate virtual CISO value and identifies areas requiring additional attention. Metrics should be meaningful to both technical staff and executive leadership.
Stakeholder Satisfaction and Engagement
Monitor stakeholder satisfaction throughout the implementation process to ensure your virtual CISO effectively meets organizational needs. This includes feedback from IT staff, executive leadership, and other personnel who interact with virtual CISO services.
Successful virtual CISOs build strong working relationships across your organization while providing valuable security expertise and guidance. Regular stakeholder feedback helps identify relationship issues before they impact implementation success.
Consider formal feedback collection at key milestones to ensure continued alignment between virtual CISO performance and organizational expectations. This feedback supports ongoing relationship optimization and success.
Long-term Program Development
Evaluate your virtual CISO’s contribution to long-term security program development and strategic planning. Effective virtual CISOs provide both immediate security improvements and sustainable program development that continues beyond their direct involvement.
Assess whether your virtual CISO has established processes, policies, and capabilities that strengthen your security posture over time. Long-term program development should reduce your dependence on external expertise while maintaining security effectiveness.
Consider how well your virtual CISO has prepared your organization for future security challenges including emerging threats, regulatory changes, and business growth requirements. Strategic thinking and planning demonstrate virtual CISO value beyond immediate tactical improvements.
Maximizing Virtual CISO Implementation Success
Active Participation and Collaboration
Organizations that actively participate in virtual CISO implementation typically achieve better outcomes than those with passive approaches. Assign dedicated internal resources to support virtual CISO activities and ensure timely response to information requests.
Encourage open communication between your virtual CISO and internal stakeholders. Regular interaction helps build relationships, transfer knowledge, and ensure security initiatives align with business operations and culture.
Consider your virtual CISO as a strategic partner rather than an external vendor. This mindset encourages collaboration and knowledge sharing that benefits long-term security program development.
Investment in Supporting Infrastructure
Virtual CISO recommendations often require investment in security tools, training, or operational capabilities. Organizations that make appropriate investments typically achieve better security outcomes and realize greater value from virtual CISO services.
Evaluate virtual CISO recommendations objectively based on risk reduction, compliance requirements, and business value rather than simply cost considerations. Strategic security investments often provide significant return through risk reduction and operational efficiency.
Consider the total cost of security incidents, compliance failures, or operational disruptions when evaluating investment recommendations. Proactive security investments typically cost less than reactive incident response and recovery.
Continuous Improvement and Learning
Approach virtual CISO implementation as an ongoing learning and improvement process rather than a one-time project. Regular evaluation and optimization help ensure continued value and alignment with changing business needs.
Encourage knowledge transfer from your virtual CISO to internal staff to build organizational security capabilities over time. This knowledge transfer reduces dependence on external expertise while strengthening internal security competency.
Stay engaged with security program development and strategic planning to ensure continued alignment with business objectives and risk tolerance. Your active participation helps optimize virtual CISO services and maximize long-term value.
Beyond the First 90 Days: Sustainable Success
Ongoing Partnership Development
After the initial 90-day implementation period, your virtual CISO relationship should transition to ongoing strategic partnership focused on continuous security improvement and program management. This long-term partnership provides sustained value through regular assessment, planning, and optimization activities.
Expect regular security program reviews, threat landscape updates, compliance monitoring, and strategic planning sessions. Your virtual CISO should help your organization adapt to changing security requirements while maintaining alignment with business objectives.
Consider how your virtual CISO relationship may evolve as your organization grows or security requirements change. Flexible engagement models allow scaling of virtual CISO services based on changing needs and circumstances.
Building Internal Security Capabilities
Successful virtual CISO engagements should strengthen your organization’s internal security capabilities over time. This includes policy development, process improvement, staff training, and strategic planning competencies that reduce dependence on external expertise.
Work with your virtual CISO to develop internal security leadership and technical capabilities that support long-term program sustainability. This capability development represents significant value beyond immediate security improvements.
Consider whether your organization may eventually require full-time security leadership as you grow. Your virtual CISO can help prepare for this transition by developing internal capabilities and program maturity that support future hiring.
Conclusion: Realistic Expectations for Virtual CISO Success
Virtual CISO implementation success requires realistic expectations, active collaboration, and sustained commitment to security program development. Organizations that approach the engagement as a strategic partnership rather than a simple vendor relationship typically achieve better outcomes.
The first 90 days establish the foundation for long-term virtual CISO success through comprehensive assessment, strategic planning, and initial implementation activities. This period requires significant investment of time and attention from your internal team to ensure effective collaboration and knowledge transfer.
Successful virtual CISO implementations produce measurable security improvements, enhanced compliance posture, and stronger organizational security capabilities. These outcomes require sustained effort and appropriate investment in supporting infrastructure and operational changes.
Ready to begin your virtual CISO implementation journey? BlueRadius Cyber provides experienced virtual CISO services with structured implementation processes designed to deliver measurable security improvements within 90 days. Contact us for a complimentary consultation to discuss your cybersecurity requirements and implementation objectives.
Related Resources
Continue your virtual CISO research with these resources:
- How to Choose a Virtual CISO Provider: Complete Buyer’s Guide for 2025
- vCISO Cost Guide 2025: Pricing, ROI & What to Expect
- The 2025 Virtual CISO Market Landscape Report
- Virtual CISO Services Overview
- Free Cybersecurity Assessment
Contact BlueRadius Cyber:
- Phone: (800) 930-0989
- Email:
- Website: https://blueradius.io

Jeff Sowell is a cybersecurity leader with over 20 years of experience in IT and security roles at Fortune 500 companies. He has held key positions such as VP, CISO, and CPSO, serving as Head of Product Security at Ericsson North America. Jeff holds an M.S. in Computer Information Systems (Security) from Boston University and industry-recognized certifications including CISSP, CISM, and ISO 27001 Lead Implementor.
Related from the BlueRadius Library
Sourced posts on adjacent topics, ranked by tag overlap.
vCISO
AI Governance & Cybersecurity Framework: Virtual CISO Leadership Guide for 2025
Introduction: AI Governance – The New Frontier for Cybersecurity Leadership Artificial intelligence has transformed from a futuristic concept to a business-critical technology that
ReadvCISO
Port Security Virtual CISO: Protecting Houston's Critical Trade Infrastructure
The Port of Houston handles over 290 million tons of cargo annually, making it America's busiest port by tonnage and a critical gateway for global trade. This massive maritime comp
ReadvCISO
Energy Sector Virtual CISO: Cybersecurity Leadership for Dallas Oil & Gas Companies
Dallas stands as America's energy capital, home to more Fortune 500 energy companies than any other U.S. city. From ExxonMobil's global headquarters to hundreds of independent oil
ReadvCISO
What is a Virtual CISO (vCISO)? Complete Guide
Quick Answer A virtual CISO (vCISO)—also called fractional CISO, part-time CISO, or outsourced CISO—is an experienced Chief Information Security Officer who provides executive-leve
ReadvCISO
Why GRC Platforms Fail Without vCISO Guidance: The Strategic Gap in Compliance Automation
Quick Answer Modern AI-powered GRC platforms can predict risks, validate evidence quality, and automate complex compliance workflows—yet 60% of organizations still manage complianc
ReadvCISO
Virtual CISO for Manufacturing: Complete OT/IT Security Leadership Guide
Quick Answer: Virtual CISOs provide manufacturing companies with specialized operational technology (OT) and IT security leadership, ICS/SCADA expertise, and regulatory compliance
ReadRelated services